Severity
High
Analysis Summary
Microsoft 365 tenants across the Middle East have been targeted by a new password spray campaign linked to an Iran-affiliated threat actor. Unlike malware-based attacks, the operation exploited weak passwords and exposed cloud accounts to gain access to email, documents, and administrative tools. The activity occurred in three waves on March 3, 13, and 23, 2026, with the main focus on Israel and the United Arab Emirates, affecting over 300 organizations in Israel and 25 in the UAE, along with additional targets in Europe, the United States, the United Kingdom, and Saudi Arabia. The campaign encompassed government entities, municipalities, energy groups, and private companies.
Researchers assessed with moderate confidence that the actor originates from Iran, based on the sectors targeted, regional focus, and login behavior patterns. The attack leveraged password spraying, a method that tests a small set of common passwords across many accounts, rather than repeatedly targeting a single user, allowing the campaign to evade detection while quietly compromising accounts.
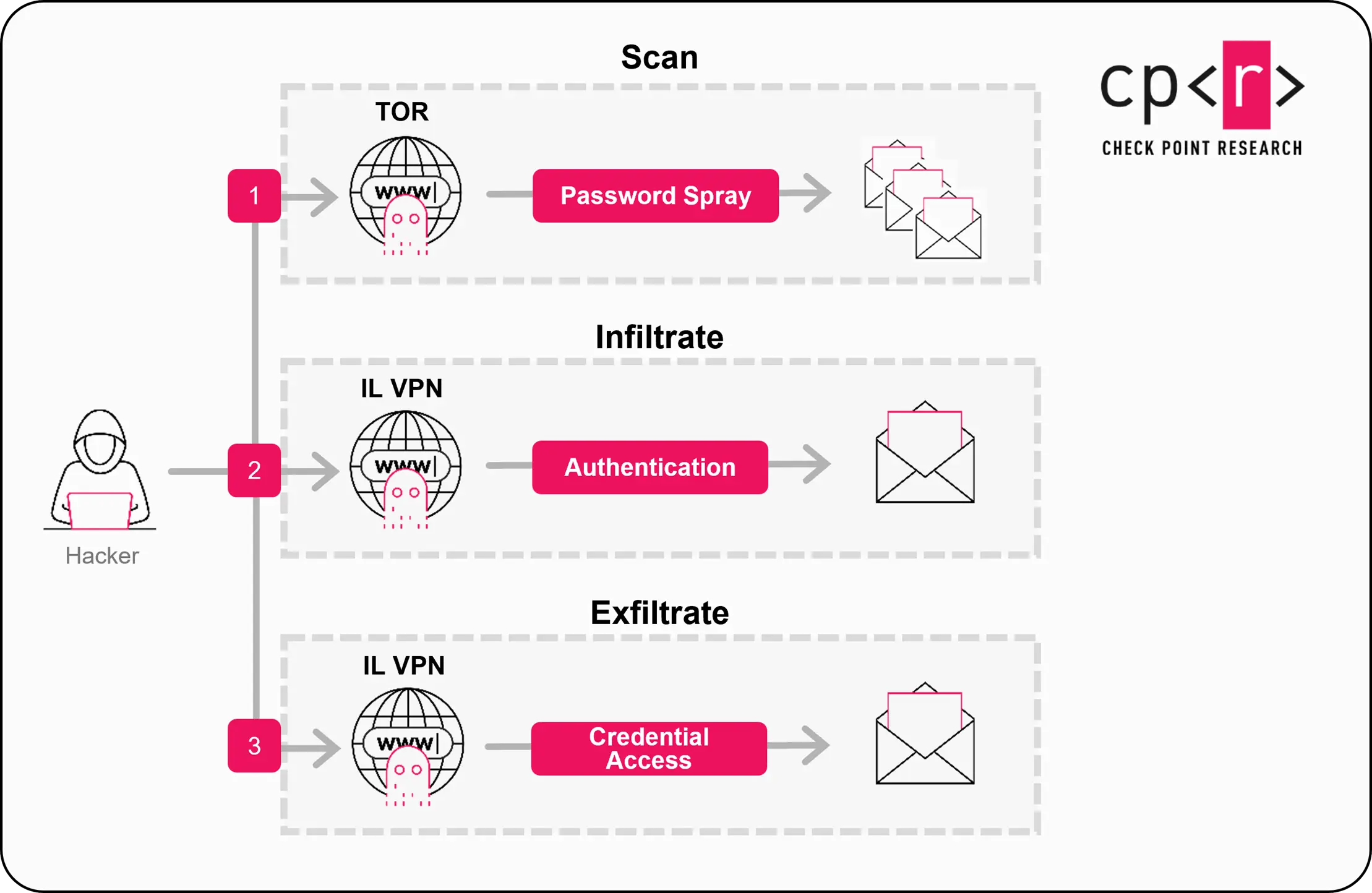
The attack cycle followed three stages: scan, infiltrate, and exfiltrate. During the scanning phase, the actor used rotating Tor exit nodes and spoofed user agents mimicking Internet Explorer 10 on Windows 7, reducing the value of single indicators. Once valid credentials were discovered, logins shifted to commercial VPN ranges like Windscribe and NordVPN, geolocated in Israel, likely to bypass geo-restrictions and avoid alerts. By exploiting valid accounts rather than deploying malware, attackers could access sensitive email and cloud data while leaving minimal noise for security teams to detect.
To mitigate this threat, organizations are urged to monitor sign-in logs for failed attempts across accounts, enforce tenant-wide multi-factor authentication (MFA), implement location-based access controls, block Tor access where feasible, improve password hygiene, and maintain audit logs for post-compromise investigations. This campaign highlights that even simple identity attacks can create serious security breaches, emphasizing that identity monitoring is as critical as endpoint protection for Microsoft 365 environments, where a single weak password can expose a broad range of services and sensitive information.
Impact
- Sensitive Data Theft
- Gain Access
Indicators of Compromise
IP
- 185.191.204.202
- 185.191.204.203
- 169.150.227.3
- 169.150.227.143
- 169.150.227.146
Remediation
- Block all threat indicators at your respective controls.
- Search for indicators of compromise (IOCs) in your environment utilizing your respective security controls.
- Enable tenant-wide multi-factor authentication (MFA) to prevent unauthorized access even if passwords are compromised.
- Monitor sign-in logs for patterns of failed login attempts across multiple accounts from a single source.
- Implement location-based access controls to restrict logins from suspicious or high-risk regions.
- Block or restrict access from Tor exit nodes and other anonymizing services where possible.
- Enforce strong password policies and improve overall password hygiene across all accounts.
- Maintain detailed audit logs for post-compromise investigation and detection of unusual activity.
- Use conditional access policies to limit access based on device compliance, network location, or risk level.
- Regularly review and disable inactive or unnecessary accounts to reduce the attack surface.

