Severity
High
Analysis Summary
Ethereum recently faced a security incident where a threat actor compromised its mailing list provider and sent a phishing email to over 35,000 addresses.
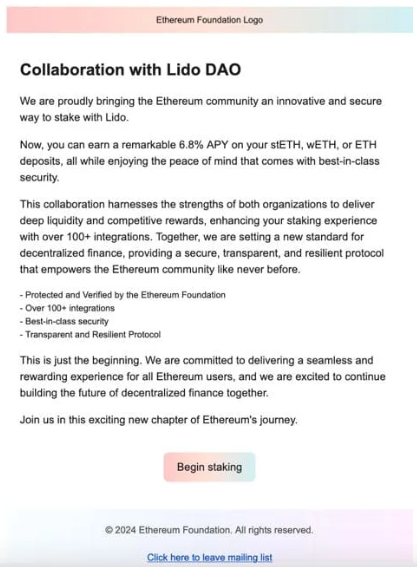
The email, sent from 'updates@blog.ethereum.org,' targeted 35,794 addresses on June 23, falsely claiming a collaboration with Lido DAO and promising a 6.8% annual percentage yield (APY) on staked Ethereum. The phishing attempt aimed to lure recipients to a malicious website where connecting their wallets and signing a transaction would result in their funds being drained by the attacker.
Despite the extensive reach of the attack, Ethereum reported no material impact on users. The threat actor used a combined email list consisting of their collection and an additional 3,759 addresses exported from Ethereum's blog mailing list. Among these, only 81 addresses were previously unknown to the attacker.
The phishing email directed recipients to a professionally crafted fake website that mimicked the legitimate promotion with a 'Begin staking' button that initiated the malicious transaction. This sophisticated setup was designed to deceive users into believing they were participating in a genuine staking offer thereby compromising their wallets.
Ethereum's internal security team responded swiftly to the breach, initiating an investigation to identify the attacker understand the attack's mechanics determine the timeline, and pinpoint affected parties. Immediate actions included blocking the attacker from sending further emails and using Twitter to alert the community about the phishing attempt. Ethereum also worked to add the malicious link to various blocklists, blocking it by most Web3 wallet providers and Cloudflare, thus preventing further potential harm.
Ultimately, on-chain transaction analysis revealed that the phishing attempt during the campaign tricked none of the email recipients. Ethereum has since taken additional security measures and is migrating some of its email services to other providers to prevent future incidents. The quick and effective response along with preventive measures highlights Ethereum's commitment to safeguarding its community from such attacks.
Impact
- Exposure of Sensitive Data
- Identity Theft
- Financial Loss
Remediation
- Use strong, unique passwords for sensitive accounts. Regularly change passwords for all accounts.
- Implement multi-factor authentication (MFA) on all accounts to add an extra layer of security to login processes.
- Organizations need to stay vigilant and follow best practices for cybersecurity to protect their systems and data from potential threats. This includes regularly updating software and implementing strong access controls and monitoring tools.
- Develop a comprehensive incident response plan to respond effectively in case of a security breach or data leakage.
- Maintain regular backups of critical data and systems to ensure data recovery in case of a security incident.
- Adhere to security best practices, including the principle of least privilege, and ensure that users and applications have only the necessary permissions.
- Establish a robust patch management process to ensure that security patches are evaluated, tested, and applied promptly.
- Conduct security audits and assessments to evaluate the overall security posture of your systems and networks.
- Implement network segmentation to contain and isolate potential threats to limit their impact on critical systems.
- Never trust or open links and attachments received from unknown sources/senders
- Improve communication with customers by providing timely and transparent updates about data breaches, including what information was compromised and the steps being taken to mitigate the impact.
- Ensure that all vendors and third-party partners adhere to stringent security protocols and regularly assess their cybersecurity practices to minimize the risk of data breaches originating from external sources.
- Provide affected customers with comprehensive support, including credit monitoring services, identity theft detection, and resolution assistance, to help mitigate the potential consequences of the breach.

