Severity
High
Analysis Summary
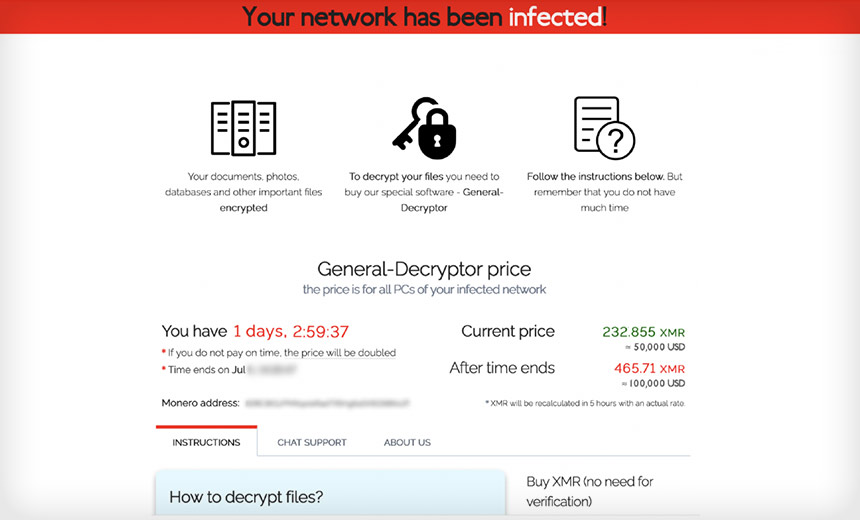
The REvil (also known as Sodinokibi) is a Ransomware-as-a-Service (RaaS). The first attack of REvil was in middle of April 2019, and attracted huge attention span from the InfoSec world due to their uncanny similarities with GandCrab Ransomware. The group uses different distribution techniques of deploying ransomware such as exploit kits, scans and exploiting various vulnerable software (Oracle WebLogic), RDP servers, and backdoored software installers. Revil has made an estimated $100 million by infecting large business owners and they threaten to publish data if the ransom money is not paid by the victim.
The ransom note placed by REvil (Source: Elliptic)
Sodinokibi ransomware can encrypt data using curve25519/Salsa20 and keys using curve25519/AES-256-CTR. The user’s private key is encrypted by the malware using two public keys. Additionally, this infection uses asymmetric key scheduling and command and control server obfuscation, which enable the malware to function without a connection to the C2.
Impact
- File Encryption
Indicators of Compromise
MD5
e018cd3014d60937d52ad867e2e5b245
SHA-256
315502122d478fe4f11b55f30cea48fb3c33af97052af35d0bc9a4e25739c376
SHA-1
840dea6f464d59f20cd19847d9c2e2364e36ad33
Remediation
- Block all threat indicators at your respective controls.
- Search for Indicators of compromise (IOCs) in your environment utilizing your respective security controls.
- Maintain cyber hygiene by updating your anti-virus software and implement patch management lifecycle.
- Maintain Offline Backups – In a ransomware attack, the adversary will often delete or encrypt backups if they have access to them. That’s why it’s important to keep offline (preferably off-site), encrypted backups of data and test them regularly.
- Emails from unknown senders should always be treated with caution.
- Never trust or open ” links and attachments received from unknown sources/senders.

