Severity
High
Analysis Summary
Lazarus APT is one of North Korea’s most sophisticated threat actors, operating since at least 2009. Initially, they concentrated on South Korea. It has recently shifted its focus to worldwide targets and began initiating assaults for monetary gain. This actor has been linked to attacks in South Korea, the United States, Japan, and a number of other nations. Lazarus APT is suspected of being behind a number of diverse efforts, including cyberespionage, attacks on financial institutions, government agencies, and the military.
This group is said to be behind the wiper attack on Sony Pictures Entertainment in November 2014 as part of Novetta’s Operation Blockbuster campaign. Lazarus Group’s malware is linked to other known campaigns such as Operation Flame, Operation Troy, DarkSeoul, Operation 1Mission, and Ten Days of Rain.
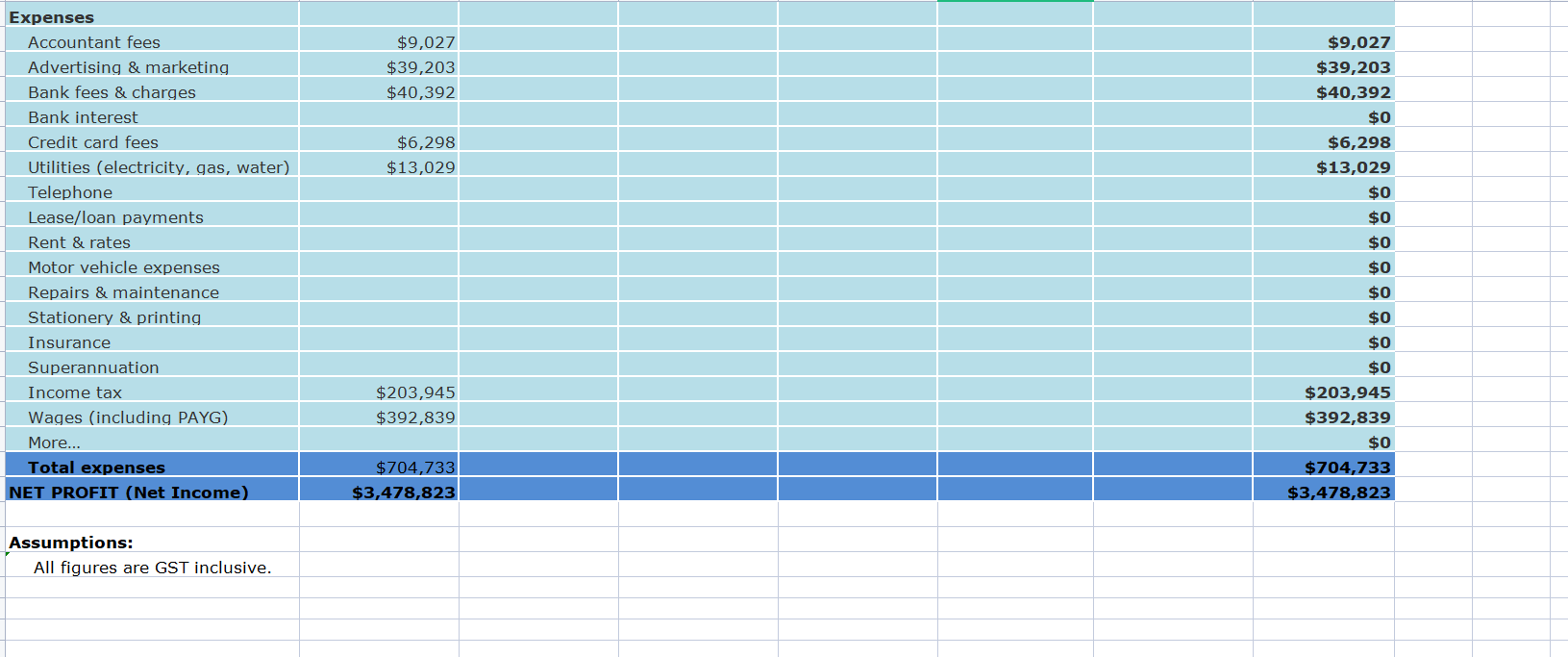
Annual P&L Statement. zip
Impact
- Information Theft and Espionage
- Exposure of Sensitive Data
Indicators of Compromise
Domain Name
- allinfostudio[.]com
- yourblogcenter[.]com
Filename
- Benefit_Job_LockheedMartin_description[.]exe
- Assist[.]lnk
- Annual P&L Statement[.] zip
MD5
- 8df7777ac7315c5e256ce35ea36cc73f
- 750b7f389dc47d73d0c77d76fbaccfc3
- c1bce93930a950f11bf631ca3b32b510
- 934c7b7c31d84728f0086be9b80ee1e4
SHA-256
- e5466b99c1af9fe3fefdd4da1e798786a821c6d853a320d16cc10c06bc6f3fc5
- 928e92a0d08fab2e19bb07601f4904f60ed265a9f030d938c5a5454b4ed69af7
- 3f01f16519c636e7b0ae5e9f01c0645d38485cb9117e2ca799ad98183437a73d
- a3a1968fefab3c9d11976f8c00a9f726e0729f8e21761247f41790b4669bfde8
SHA-1
- 7d09178e4702790ec370e50b973528aec5bf0e3a
- a553bfc196fe4aab91e4a99005e71126527e27f1
- 5e26b26cd5f6b7509a2870bb63bd1ff553a5cc90
- 18e4203dab96fefd1b2c0c7e653b354fb3d27add
URL
- hxxp[:]//www[.]docusign[.]agency/1
- hxxp[:]//www[.]docusign[.]agency/2
- https[:]//www[.]docusign[.]agency/WG70GuIDhXvWk3S/fCfLkC7ZY+OrTXcMwgTMH51xNzM=
- https[:]//www[.]docusign[.]agency/jZqVFMZ9mf2WF5TkgEeGRZ2si09QqjBAcdHN46XpjRs=
- https[:]//drive[.]cloudplus[.]one/xg/XjyZ4liSxPxR8N07y5jfDBK7JxlNhTOM0rkJaZ8w=
Remediation
- Always be suspicious about emails sent by unknown senders.
- Never click on links/attachments sent by unknown senders.
- Block all threat indicators at your respective controls.
- Search for IOCs in your environment.

