Severity
High
Analysis Summary
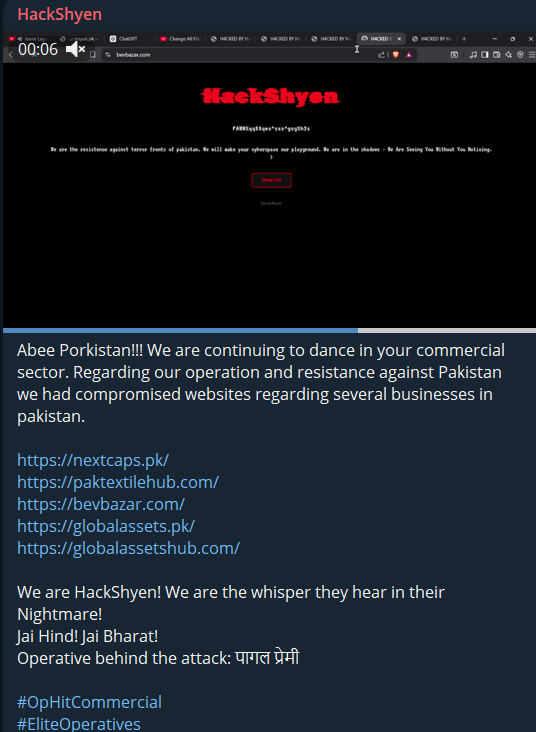
An Indian hacktivist group, HackShyen, has claimed responsibility for a large-scale cyber campaign targeting Pakistan’s critical national infrastructure (CNI) and commercial sector.
According to multiple statements released by the group, they have developed and deployed an advanced exploitation framework capable of identifying and attacking over 400 industrial control systems (ICS), including technologies such as Modbus, DNP3, and Siemens-based environments.
The framework reportedly leverages Shodan Enterprise API to automate the discovery of internet-exposed and vulnerable ICS devices. Once identified, the tool executes a multi-phase attack chain involving scanning, exploitation, and destructive modules. A key capability includes Modbus coil manipulation, which allows attackers to remotely switch industrial equipment on or off. This poses significant risks to real-world operations, including potential disruptions to electricity supply, water distribution systems, and industrial manufacturing processes.
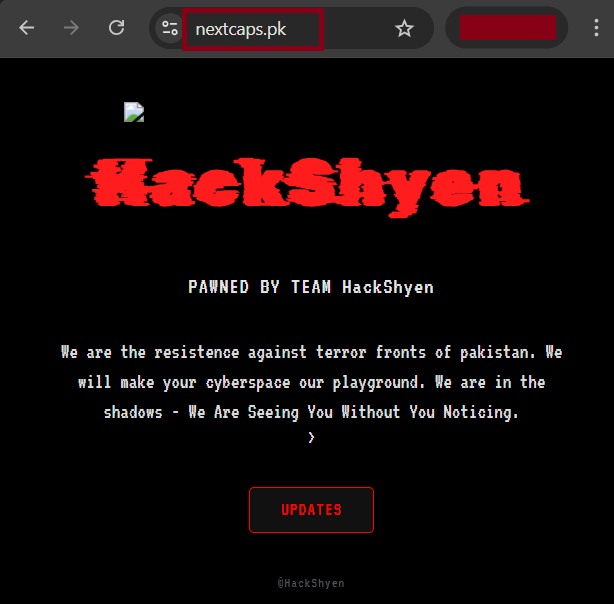
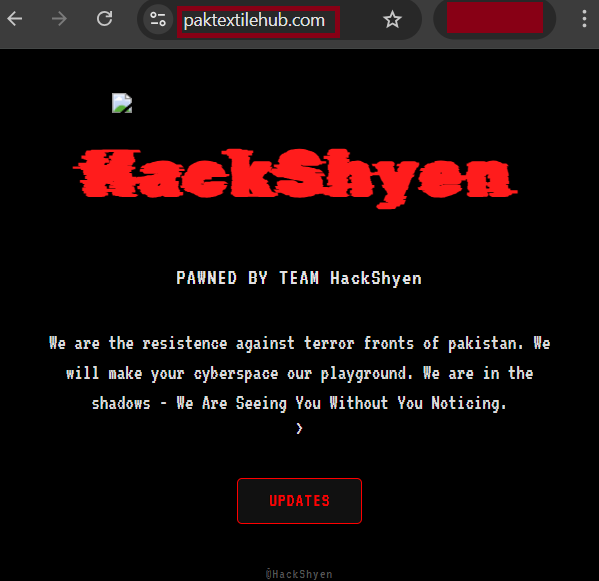
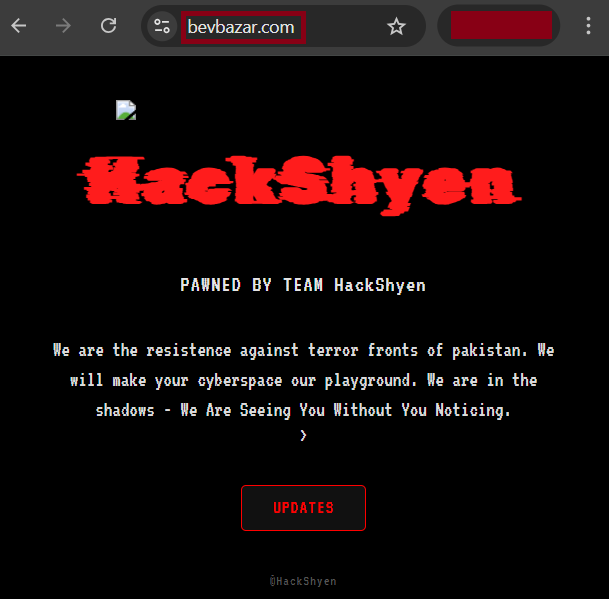
HackShyen has also claimed successful compromises within Pakistan’s commercial sector, including defacement or unauthorized access to several business websites such as:
- https://nextcaps[.]pk/
- https://paktextilehub[.]com/
- https://bevbazar[.]com/
These activities are being promoted under coordinated campaigns such as “BlackOutOp2026” and “Revolutionize Indian Hacktivism,” with the group distributing the framework freely to expand participation among aligned hacktivists.
The group emphasizes that this operation goes beyond traditional cyberattacks like website defacement, highlighting its potential to cause physical and operational disruptions. If validated, such capabilities could lead to power outages, halted water supply, and shutdown of critical industrial processes. Overall, these claims suggest a shift toward more impactful, infrastructure-focused hacktivism.
Impact
- Reputational Damage
- Operational Disruption
- Unauthorized Access
Remediation
- Restrict external exposure of ICS assets identified through threat intelligence feeds and continuously validate against sources like Shodan to detect publicly accessible systems
- Correlate SIEM alerts with TI indicators (IP addresses, domains, scanning patterns) to detect reconnaissance and exploitation attempts in early stages
- Block known malicious IPs, TOR exit nodes, and suspicious ASN ranges at perimeter firewalls based on curated threat intelligence feeds
- Monitor for abnormal ICS protocol activity (e.g., Modbus coil write commands) and trigger high-severity alerts for unauthorized command execution
- Enforce network segmentation and validate through continuous SOC monitoring to ensure no unauthorized IT-to-OT communication paths exist
- Integrate Endpoint Detection and Response (EDR) and Network Detection and Response (NDR) tools with SOC workflows for real-time threat visibility
- Implement use-case driven detection rules in SIEM for behaviors such as mass scanning, brute-force attempts, and unauthorized remote access
- Conduct proactive threat hunting campaigns focusing on ICS exploitation patterns and known TTPs used by hacktivist groups
- Maintain and update IOC repositories regularly, ensuring enrichment with context (geolocation, reputation, behavior patterns)
- Establish automated alert triage and escalation procedures within SOC to reduce response time for critical infrastructure threats
- Perform continuous log collection from OT gateways, firewalls, and ICS devices, ensuring centralized visibility in SIEM
- Validate alerts against MITRE ATT&CK techniques relevant to ICS (e.g., impact, lateral movement, command execution) for structured analysis
- Conduct regular purple team exercises simulating ICS-targeted attacks to test SOC detection and response capabilities
- Share intelligence internally and with trusted external partners (ISACs, CERTs) to enhance situational awareness and collective defense


