Severity
High
Analysis Summary
A threat actor named as penguinbrew has claimed to leak a database belonging to FoodPapa.pk, a Pakistani food delivery platform. The data is reportedly sourced from a January 2026 backup, indicating a potential large-scale exposure.
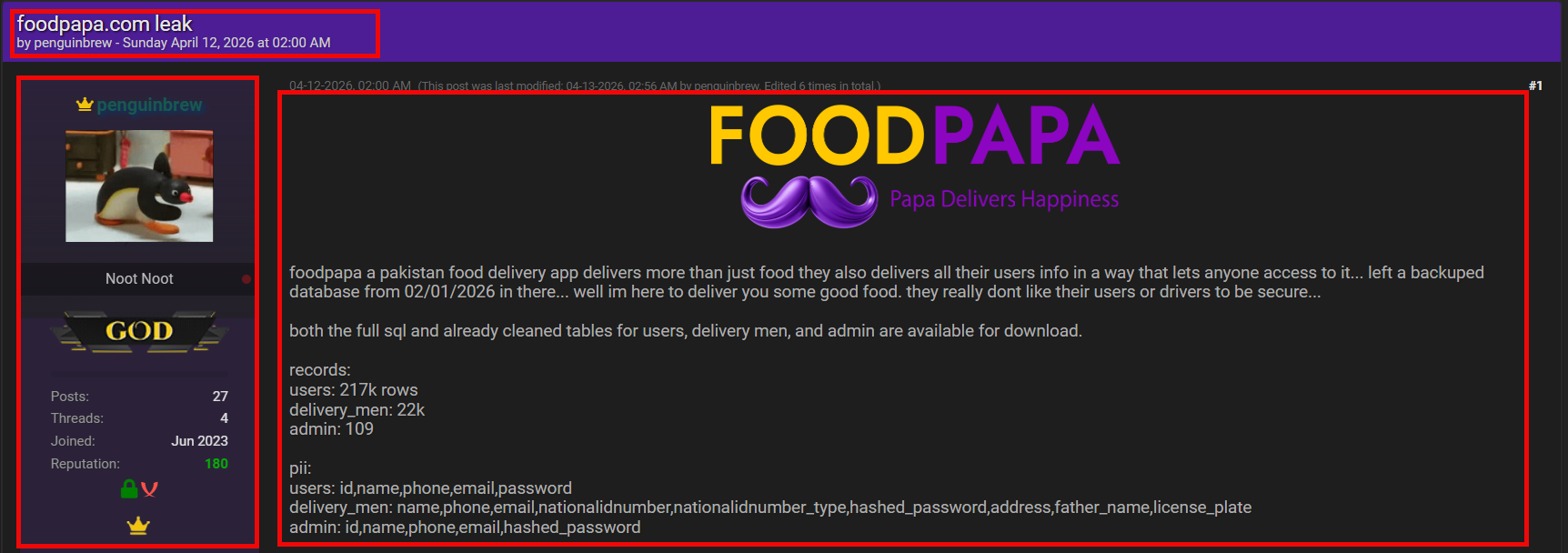
The breach allegedly impacts around 217,000 user accounts, exposing a significant portion of the platform’s customer base and raising concerns over widespread personal data compromise.

In addition, approximately 22,000 delivery driver accounts and administrative records are claimed to be included, increasing the severity due to operational and privileged data exposure.
The exposed data allegedly contains a wide range of sensitive information. This includes full names, phone numbers, email addresses, and bcrypt-hashed passwords. More critically, authentication-related data such as JWT tokens, Firebase tokens, API credentials, and refresh tokens were also reportedly included. In addition, highly sensitive personal data such as CNIC numbers, home addresses, family details, and driver-specific information like vehicle and license plate details were part of the leak.
The presence of authentication tokens and API credentials significantly elevates the risk, as these could enable session hijacking or unauthorized backend access if still valid. The exposure of CNIC and personal identity data increases the likelihood of identity theft, fraud, and targeted social engineering attacks.
From a threat intelligence perspective, the incident appears to stem from a misconfigured system or an exposed database backup. The inclusion of both user and administrative data further amplifies the potential impact.
Although the breach remains unverified, it presents serious risks, including phishing campaigns, account takeovers, and abuse of platform infrastructure if the leaked credentials are active.
Impact
- Identity Theft
- Unauthorized Access
- Reputational Damage
- Sensitive Information Disclosure
Remediation
- Invalidate all active sessions and tokens to prevent session hijacking
- Reset passwords for all users and enforce strong password policies
- Rotate API keys, JWT secrets, and all exposed credentials immediately
- Enable multi-factor authentication (MFA) for users, drivers, and admins
- Patch and secure any misconfigured databases or exposed backups
- Conduct a full security audit to identify and close vulnerabilities
- Encrypt sensitive data at rest and ensure proper key management
- Monitor logs and network activity for suspicious behavior or abuse
- Implement rate limiting and anomaly detection to prevent automated attacks
- Notify affected users and advise them on security precautions
- Restrict access using least privilege principles across all systems
- Regularly back up data securely and avoid storing sensitive data unnecessarily


