Severity
High
Analysis Summary
The STOP/DJVU ransomware initially made headlines in 2018 and has since been attacking individuals all around the world. It’s widespread on torrent sites and other platforms in software crack packages and adware bundles. DJVU Ransomware is a type of malicious software that encrypts files on an infected computer and demands a ransom payment in exchange for the decryption key. The STOP/DJVU Ransomware family is one of the most prevalent ransomware threats and is known for its aggressive tactics and high-pressure ransom demands.
Malware is delivered via cracked applications, fake set-up app keygens, activators, and Windows updates. It does not utilize local information like keyboard layouts or timezone settings to prevent infecting victims in certain countries; instead, it uses the information returned by a request to https[:]//api.2ip.ua/geo.json. The card’s MAC address is utilized to provide unique identification for the system. This identity is provided to STOP’s command and control server, which responds with an RSA-2048 public key for encryption. Additional malware, including an information stealer known as Vidar, is then downloaded and installed.
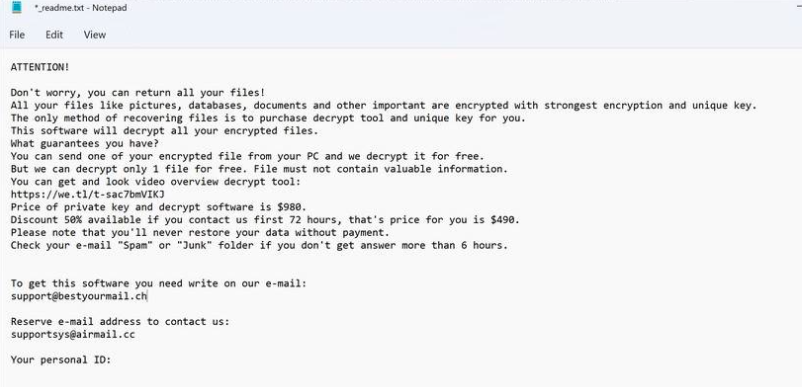
ransom note
Impact
- Information Theft
- File Encryption
Indicators of Compromise
MD5
- de93e8a0692db2c2f178270b8da7b5d7
- 3eeb7b2030517f91fdf0f4c5278d8e76
- 1a3bb5acfb7f3ee075b7e6bd97243935
- de8d1752bf8dd628a5065c19f83af296
- 9de69c7a3e551dcbc9208221099680a7
- afdd799a769a2fd3f66c2fad9f1d1026
- 14a5973627a876bdbafb029a26084f64
SHA-256
- 1ca8ad78274a829697b8381e96b914fea1a65b5b2351f536325d2143d689426e
- 4ad7b8d228fe32d82b0373ce886f224f47c2e06a59d394c634160c70083b5f32
- b7e8263a9210b8d4b85e957fd5cf0d23626926f7e41c1df3bbe468d12609d6e6
- 1c1db50e2876a312fc1b8cf6f3234d157f7accc140b14b47318c735d97693f3b
- 9a880d7572486dd985ed6ffbf55eee8875077d9614befc12d5fbdaafd45e86d5
- c96ebdb12684d0b47ebd0fa81aee556c8c981b942262d2169d9f63dc3b7e5a7c
- bd2b3bc973155b2f6b0866245d933619550d127f292cb912e9cea106fb8392a5
SHA-1
- 21df7a70852c9d47b3423d14005bf67a69e6fdcc
- c4c3a4650d278f2f8b9bf871c2ae91508ffae165
- f2552378ab103181e6936a074a5dbdb2bdca06f5
- c774109e88b1c71a1f3c92f1dbb04a3151b45966
- e5ae2554407774c2cbbdde1c1dca1b15d51b6d20
- b08ec120f594b4b3c972a52bb4e7be343a62ef25
- 5514e9a9d8806406ff9921c9be25bd1e314b0b9b
Remediation
- Block all threat indicators at your respective controls. Search for Indicators of compromise (IOCs) in your environment utilizing your respective security controls.
- Enabling two-factor authentication (2FA) on your accounts adds an extra layer of security and can help prevent unauthorized access even if your login credentials have been stolen.
- Regularly backing up your important data can help ensure that you don’t lose any critical information in the event of a malware infection or other data loss event.
- Be wary of emails, attachments, and links from unknown sources. Also, avoid downloading software from untrusted sources or clicking on suspicious ads or pop-ups.
- Make sure all of your software, including your operating system and applications, is up-to-date with the latest security patches. This can help prevent vulnerabilities that could be exploited by info-stealers and other types of malware.

