Severity
High
Analysis Summary
Mallox is a ransomware strain that specifically targets Microsoft (MS) Windows systems and has been active since June 2021. It is known for its exploitation of unsecured MS-SQL servers as a penetration vector to gain access to victims’ networks.
According to new findings from researchers, Mallox ransomware activities in 2023 have surged by 174% compared to the previous year. Similar to other ransomware threat actors, Mallox follows the double extortion trend, where it first steals sensitive data from organizations before encrypting their files. It then uses the threat of leaking the stolen data on a public leak site to put pressure on victims to pay the ransom fee.
Mallox is associated with a threat actor that has ties to several other ransomware strains, including TargetCompany, Tohnichi, Fargo, and the latest addition, Xollam. The ransomware first gained attention in June 2021 and has been focused on targeting significant sectors, such as manufacturing, professional and legal services, and wholesale and retail industries.
One notable aspect of the group is its pattern of exploiting poorly secured MS-SQL servers through dictionary attacks to compromise victims’ networks. Xollam, however, deviates from this norm and has been observed using malicious OneNote file attachments for initial access, as reported by Trend Micro.
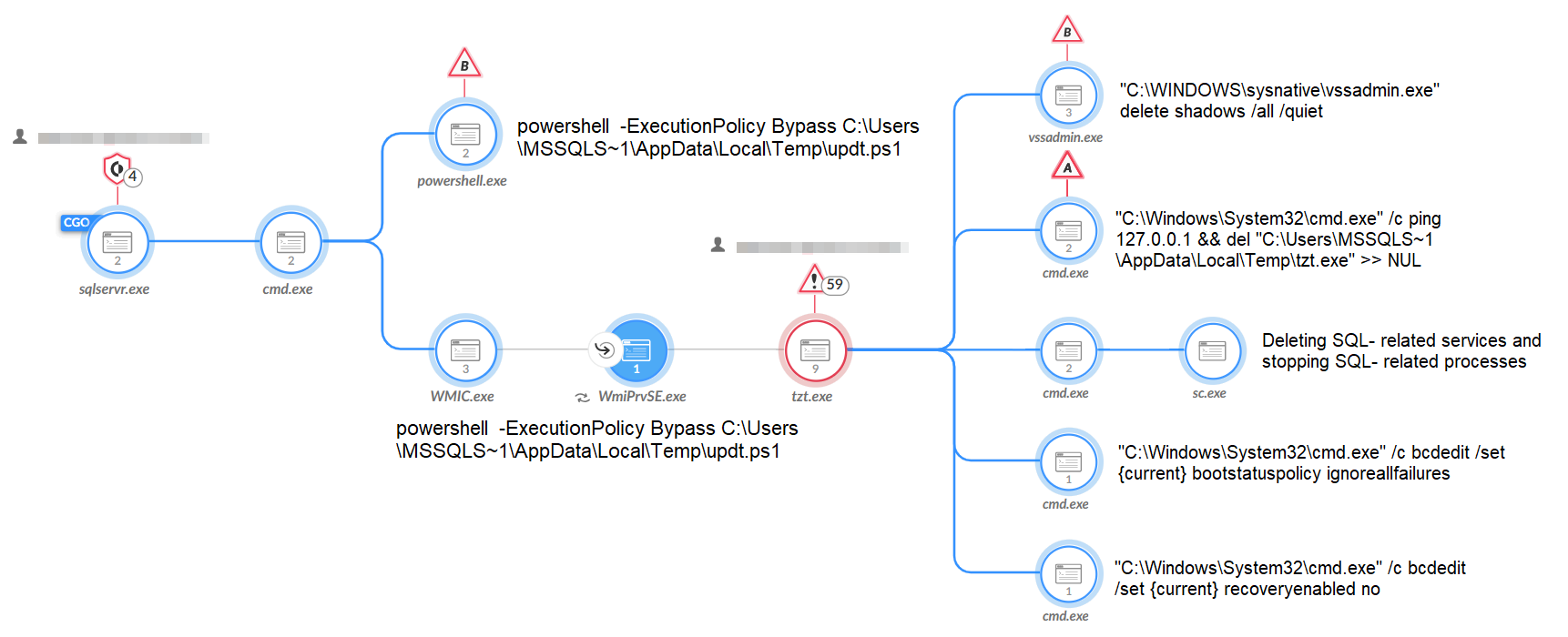
After gaining a foothold on an infected host, Mallox executes a PowerShell command to retrieve the ransomware payload from a remote server. The ransomware binary then attempts to disable SQL-related services, delete volume shadow copies, clear system event logs, terminate security-related processes, and bypass Raccine, an open-source tool designed to counter ransomware attacks. Following this, the encryption process begins, and a ransom note is deposited in every directory.
TargetCompany, while a small, closed group, has been observed recruiting affiliates for the Mallox ransomware-as-a-service (RaaS) program on the RAMP cybercrime forum, hinting at potential expansion of their operations.
“The Mallox ransomware group has been more active in the past few months, and their recent recruiting efforts may enable them to attack more organizations if the recruitment drive is successful.”, they added.
The sudden rise in Mallox infections is part of a broader trend of ransomware attacks, which have experienced a 221% year-over-year increase as of June 2023. In June 2023 alone, there were 434 reported attacks, primarily driven by Cl0p’s exploitation of the MOVEit file transfer software vulnerability.
“The team recommends making sure that all internet-facing applications are configured properly and all systems are patched and up to date wherever possible. These measures will help to reduce the attack surface, thereby limiting the exploitation techniques available to attackers.”
Security researchers have warned that Mallox’s recent recruitment efforts may lead to more successful attacks on organizations, given the current increase in ransomware activities. The ongoing trend of ransomware
Impact
- File Encryption
- Sensitive Information Theft
- Unauthorized Access
Indicators of Compromise
MD5
- 6ea65106bdd4ab1148028f83956336d1
- 57c683e8ab7b7e1390c037c9a97c7688
- f7cbc00aaa716599bcf6a24f65b3302e
- 2f82436e491b17c67a3ea0419f0b61de
- 4f351910b30c279944615955228db869
- 06e7ad104aef0633e4817e1159851d16
- 67fd732ee69588cb09b316346bc61ee1
- e3e3cb71fec15b86e8c34c5aae2681a7
- ba1d4e9366de6b9a16fb2ef143d66b3d
- 6845db47108d6324b9fcad6707cfcff6
- da3f02b82e982f5ce5a71d769a067f3b
- 6e0ff5cdd9085463451709a8e462470f
- 3e7b527b02f4c9d8e73b2dedffbe6519
- be3537fdcf8dc04150a3ae4ad6daf9f7
- 44ebe5670496f7aa3d5bae72e938670d
- 58e47c0aff8659e8c4e4bcbed924ed45
- 86424c9f1797d280c0fe30ab813eb1da
- 1b30d16d3e632130ced6dc8b403d4275
- ecc918fd6e040ba4675c3179f05da459
SHA-256
- c599bebc9ae54a54710008042361293d71475e5fbe8f0cbaceb6ee4565a72015
- 060ed94db064924a90065a5f4efb50f938c52619ca003f096482353e444bd096
- 90be90ad4fb906574f9e7afe587f0826a71152bfc32cfc665a58877562f2edd4
- 1b2727af9fc187cd5c932c6defe50b983ad7508b4196ad6c5ff5e96686277c56
- a9543bc9612276863fc77b663fa3ff6efb85db69a01baa86c6dfabf73684b5c1
- 4e00f3e0e09d13e76da56009173098eefafc4ad50806583d5333990fa44e6420
- 6c109d098a1f44017f3937a71628d9dbd4d2ca8aa266656ee4720c37cc31558e
- 7f8f1afa1390246409263e606aa05e2896b8d1da7018c534e67ca530a59ebda1
- 8e54c38bc3585c3163c3e25d037bcf55695c274aaea770f2f59f0a0910a4b572
- 724aa6dae72829e9812b753d188190e16fb64ac6cd39520897d917cfdccc5122
- 7164ba41639c8edcd9ff1cf41a806c9a23de566b56a7f34a0205ba1f84575a48
- 0e1c7ea4148e7473e15a8e55413d6972eec6e24ef365e9f629884f89645de71a
- 4ed74a205fad15c843174d7d8b30ae60a181e79f31cc30ebc683072f187e4cdd
- ee6fd436bf5aff181e3d4b9a944bf644076e902a1bbf622978b5e005522c1f77
- ebdcf54719cceddffc3c254b0bfb1a2b2c8a136fa207293dbba8110f066d9c51
- 9a3050007e1c46e226e7c2c27d4703f63962803863290449193a0d0ca9661b3b
- d6c51935d0597b44f45f1b36d65d3b01b6401593f95cb4c2786034072ad89b63
- 586d4f86615cb3a8709ae1c08dde35087580814c1d1315af3d7b932639ff48e0
- 8e974a3be94b7748f7971f278160a74d738d5cab2c3088b1492cfbbd05e83e22
SHA-1
- a1e0b3255718cd3478e6a585305427a8f2f3133d
- 316e4c90085677c5a5f9ccb66ec64c701a89afc7
- ea2d7a7b46c02a406fc2c0e9340e2ca3f82339e3
- 8e9e1a62762255f991df8d39d19f556d47debfee
- 8c88ba08ca218bb994dbb914bb7b0df39bd445ea
- e39bf90a383548311753a116c346b47a0d63ad9d
- f40f54c139277019cf58ef57469af6794bed7e94
- b975715096aeb7740ce4a9fb86004262b0bdda80
- 5ae0e6d572dd69662dba7da5884cc4d30c2d42ee
- 2dc793dc4e5452cfe91887e9f7f65fb918e7d302
- e165cac5ab2b2312f7ed8569c69a75bae48b8316
- 751bb9e23d50a4c15f806ab62421b72912038e1a
- db4d167c06270ed8ca86024efe5646326f4ed049
- 2c3c80e650eea3084396932032cb680deb172c7f
- 1a577a294c94e9218ffdc830a2758813046a02d6
- 3119366ed5d7dab6c8b63b0770a0d996c0f1088d
- 920fe5593f81d105dc2ea7f061c02d898fdb3487
- 10ddbc228c564940d22a1b0424aeb55b48b4c0f7
- b372124021c93ffc52e43a7af0883e880d4eb730
Remediation
- Block all threat indicators at your respective controls.
- Search for Indicators of compromise (IOCs) in your environment utilizing your respective security controls
- Maintain cyber hygiene by updating your anti-virus software and implementing a patch management lifecycle.
- Maintain Offline Backups – In a ransomware attack, the adversary will often delete or encrypt backups if they have access to them. That’s why it’s important to keep offline (preferably off-site), encrypted backups of data and test them regularly.
- Keep all software and operating systems up-to-date with the latest security patches. Vulnerabilities in software can be exploited by threat actors to gain access to your systems.
- Segment your network into smaller, isolated subnetworks to limit the spread of malware in case of a breach.
- Enforce strong password policies and implement multi-factor authentication (MFA) to prevent unauthorized access to sensitive systems and data.
- Deploy robust email security solutions that can detect and block phishing attempts and malicious attachments.
- Educate employees about the risks of phishing emails and social engineering tactics. Teach them to recognize and report suspicious activities.
- Use advanced endpoint protection tools that can detect and block malicious activities on endpoints.
- Implement web filtering solutions to block access to known malicious websites and prevent users from accidentally downloading malware.
- Set up robust security monitoring and intrusion detection systems to detect unusual activities and respond promptly to any potential threats.
- Develop a comprehensive incident response plan that outlines the steps to be taken in case of a ransomware attack. Test and update the plan regularly.
- Conduct regular security audits and penetration testing to identify and address vulnerabilities proactively.
- Disable or remove unnecessary services and applications to minimize the attack surface.
- If using Remote Desktop Protocol (RDP), ensure that it is configured securely and protected with strong passwords and MFA.
- Stay informed about the latest ransomware trends and tactics to better prepare against emerging threats.

